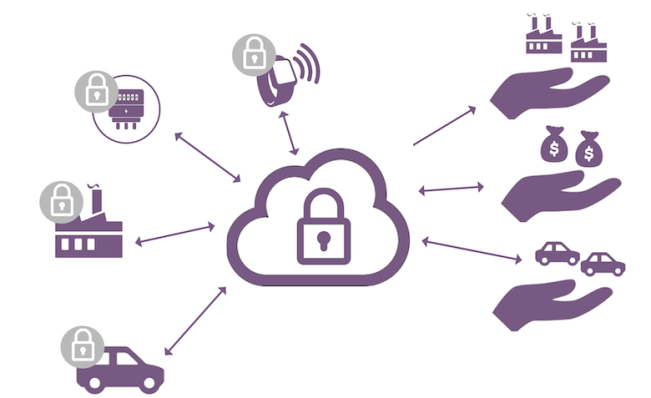
The last couple years have seen the introduction of a large numbers of IoT platforms looking to connect devices, analyze data and dispatch processed information to business applications. Unlike the previous generation of M2M systems, most of those IoT platforms are cloud- based, and have indirect control or oversight over the devices themselves. IoT solution vendors generally rely on partners to connect objects to the cloud and to make sure that edge components are secure.
A secure element running Java Card can play a critical role to ensure trust between the cloud and connected device. It can be leveraged by the device to delegate the provisioning of device identity and to manage the initial on-boarding process. It can further secure the cloud authentication and authorisation process and store the related credentials securely.
Related to the advent of cloud platforms is a growing need for the management of device lifecycle states and local enforcement of security policies.
In a market where connected objects are likely to outlive several generations of IoT systems, control over the lifecycle of a device is key to ensure that it can be retired or repurposed securely, and that it continues to align with security policies as they evolve.
Since many objects may be intermittently connected to the network, it also helps to have a secure local focal point for the administration and enforcement of security policies.
Java Card can support this use case by combining the flexibility and updatability of Java with the local enforcement capabilities of a secure element.
> Back to IoT Use Case Overview
> Find out more about Trusted Peripherals
> Download our FREE Whitepaper to find out more about how Java Card can secure the IoT sector
You must be logged in to post a comment.